Quick deployment of MS Active Directory in AWS

Were you trying to deploy a Windows Active Directory (AD) in AWS? Maybe you are here because you just tried that using the CloudFormation template referred to in this AWS post (Enabling Federation to AWS Using Windows Active Directory, ADFS, and SAML 2.0), and it failed with the following error:
API: ec2:RunInstances Not authorized for images: [ami-003a480a3489b1c5c]
If you are in a hurry, below, you can find a version of this template that includes a fix and some other minor improvements like support to deploy in a non-default VPC. And please, feel free to read the rest of this post to find out what was wrong with the original template, how to fix it, and the improvements.
CloudFormation template: https://public-cf-templates.s3.amazonaws.com/windows-active-directory/Windows_Single_Server_Active_Directory.template.json
Full story
I was looking for help to have an AD working on AWS to perform a proof of concept on a Single Sign On solution based on Cognito + SAML 2.0 and + Active Directory Federation Services (ADFS). Windows administration is not my thing, so I was looking for a shortcut to start with a working Active Directory installation. In that search, I found the following post that explains how to get an AD up and running quickly; it failed.
Original post: Enabling Federation to AWS Using Windows Active Directory, ADFS, and SAML 2.0: https://aws.amazon.com/blogs/security/enabling-federation-to-aws-using-windows-active-directory-adfs-and-saml-2-0/
What was wrong with the original CF template?
The AMI IDs embedded in the template are outdated. The original post is from 2013, yep, nine years old. Maybe you are thinking, how can I trust an ancient post like that? Ok, you are right; you can expect this ancient blog post to point you to a broken CF template. I got that. But what happens if I tell you that the CloudFormation web console also has a link to the same broken template? Here it is:
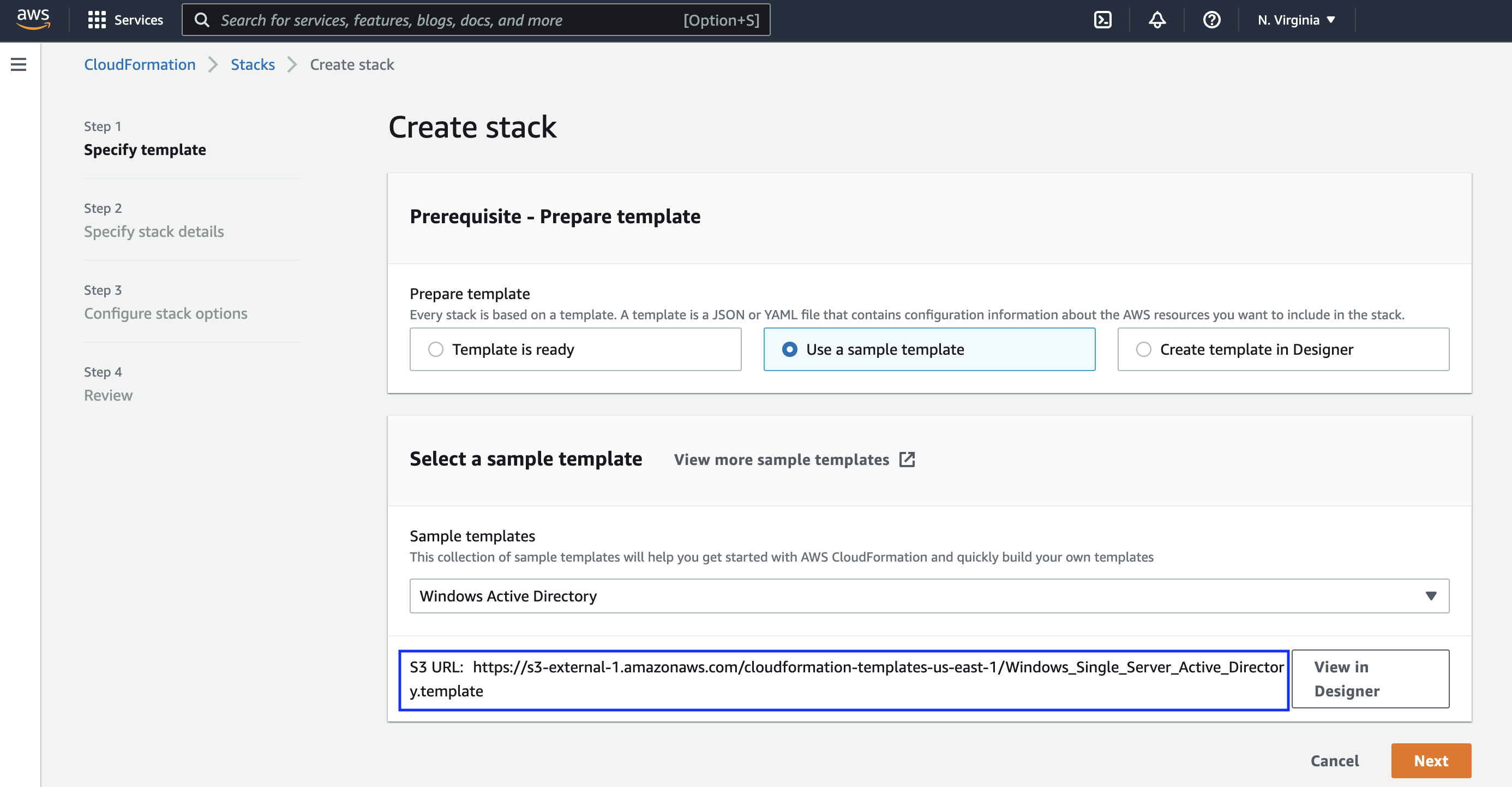
In the case of the web console, it's using a different S3 endpoint, but it's pointing to the same template in the same bucket.
Link 1 - Found in the blog post: https://s3.amazonaws.com/cloudformation-templates-us-east-1/Windows_Single_Server_Active_Directory.template
Link 2 - Found in CloudFormation Web Console: https://s3-external-1.amazonaws.com/cloudformation-templates-us-east-1/Windows_Single_Server_Active_Directory.template
How to fix it?
To fix it, you need to edit the template and add an updated AMI id. You can get the AMI ID from the EC2 launch wizard or the AWS CLI. Here is an example to list the latest Windows Server 2022 images in the North Virginia region. You can use CloudShell to run the following command:
# Listing Windows Server 2022 AMIs on the us-east-1 region:
aws ec2 describe-images --owners amazon --filters "Name=name,Values=Windows_Server-2022*" --query 'sort_by(Images, &CreationDate)[].[ImageId, Name, Description]' --region us-east-1 --no-include-deprecated
Note: I removed the AMI mapping on my version of the template. It defaults to Windows Server 2022 English Full Base in the us-east-1 region. You can get the AMI you need by running the AWS CLI command above.
Still failing, no default VPC
I fixed the AMI ID issue, but the template is still not working. Now what? Well, a limitation that I found is that the original template only works on accounts with a default VPC. In my scenario, the VPC is shared from another account, so I don't have a default VPC.
To solve the default VPC issue, I included two new parameters in the template. These are the VPC and Subnet parameters where you can specify the network to deploy the template's resources.
Then, I faced another issue related to how the security groups are created. The original template relies on the property SourceSecurityGroupName when creating the SecurityGroupIngress rules. But that is not compatible with a non-default VPC. I replaced it with SourceSecurityGroupId.
Defining the instance type
The EC2 Instance Type parameter is no more than a preconfigured list of allowed values. This approach is vulnerable to aging as new types of instances are released, so I converted it into a string with m5.large as the default value. I believe that if you are still reading this, you are very familiar with the EC2 instance types, and you can change the parameter to any other valid value.
I hope this post has helped you get an Active Directory and un running in AWS. I'm not pretending to use this template in production, but it can be handy when testing things. Enjoy! 🙂
Other resources:
Active Directory Domain Services on the AWS Cloud - Quick Start Reference Deployment
Query for the Latest Windows AMI Using Systems Manager Parameter Store

